openvpn_inc wrote: ↑Tue Nov 15, 2022 10:35 am
Hi,
It would help if you provide logs from the working and non-working situation. Also would be nice if you could answer if you really use those two subnets that collide with the VPN server subnet. Subnet collission are usually a problem anyhow.
Kind regards,
Johan
I suggest you test according to my configuration (community client - 2.5.8). Some errors occur only during the first connection and disappear the second time. I only copy the second error log.
log(community client - 2.5.8):
2022-11-15 21:37:32 DEPRECATED OPTION: --cipher set to 'AES-256-CBC' but missing in --data-ciphers (AES-256-GCM:AES-128-GCM). Future OpenVPN version will ignore --cipher for cipher negotiations. Add 'AES-256-CBC' to --data-ciphers or change --cipher 'AES-256-CBC' to --data-ciphers-fallback 'AES-256-CBC' to silence this warning.
2022-11-15 21:37:32 OpenVPN 2.5.7 [git:release/2.5/3d792ae9557b959e] Windows-MSVC [SSL (OpenSSL)] [LZO] [LZ4] [PKCS11] [AEAD] built on Oct 28 2022
2022-11-15 21:37:32 Windows version 10.0 (Windows 10 or greater) 64bit
2022-11-15 21:37:32 library versions: OpenSSL 1.1.1o 3 May 2022, LZO 2.10
2022-11-15 21:37:32 MANAGEMENT: TCP Socket listening on [AF_INET]127.0.0.1:25340
2022-11-15 21:37:32 Need hold release from management interface, waiting...
2022-11-15 21:37:33 MANAGEMENT: Client connected from [AF_INET]127.0.0.1:25340
2022-11-15 21:37:33 MANAGEMENT: CMD 'state on'
2022-11-15 21:37:33 MANAGEMENT: CMD 'log on all'
2022-11-15 21:37:33 MANAGEMENT: CMD 'echo on all'
2022-11-15 21:37:33 MANAGEMENT: CMD 'bytecount 5'
2022-11-15 21:37:33 MANAGEMENT: CMD 'state'
2022-11-15 21:37:33 MANAGEMENT: CMD 'hold off'
2022-11-15 21:37:33 MANAGEMENT: CMD 'hold release'
2022-11-15 21:37:37 MANAGEMENT: CMD 'username "Auth" "shilh"'
2022-11-15 21:37:37 MANAGEMENT: CMD 'password [...]'
2022-11-15 21:37:37 Outgoing Control Channel Encryption: Cipher 'AES-256-CTR' initialized with 256 bit key
2022-11-15 21:37:37 Outgoing Control Channel Encryption: Using 256 bit message hash 'SHA256' for HMAC authentication
2022-11-15 21:37:37 Incoming Control Channel Encryption: Cipher 'AES-256-CTR' initialized with 256 bit key
2022-11-15 21:37:37 Incoming Control Channel Encryption: Using 256 bit message hash 'SHA256' for HMAC authentication
2022-11-15 21:37:37 TCP/UDP: Preserving recently used remote address: [AF_INET]192.168.239.133:1194
2022-11-15 21:37:37 Socket Buffers: R=[65536->65536] S=[65536->65536]
2022-11-15 21:37:37 UDP link local: (not bound)
2022-11-15 21:37:37 UDP link remote: [AF_INET]192.168.239.133:1194
2022-11-15 21:37:37 MANAGEMENT: >STATE:1668519457,WAIT,,,,,,
2022-11-15 21:37:37 MANAGEMENT: >STATE:1668519457,AUTH,,,,,,
2022-11-15 21:37:37 TLS: Initial packet from [AF_INET]192.168.239.133:1194, sid=0a84d94c fa6799a6
2022-11-15 21:37:37 WARNING: this configuration may cache passwords in memory -- use the auth-nocache option to prevent this
2022-11-15 21:37:37 VERIFY OK: depth=1, CN=OpenVPN CA
2022-11-15 21:37:37 VERIFY KU OK
2022-11-15 21:37:37 Validating certificate extended key usage
2022-11-15 21:37:37 ++ Certificate has EKU (str) TLS Web Server Authentication, expects TLS Web Server Authentication
2022-11-15 21:37:37 VERIFY EKU OK
2022-11-15 21:37:37 VERIFY OK: depth=0, CN=OpenVPN Server
2022-11-15 21:37:37 Control Channel: TLSv1.3, cipher TLSv1.3 TLS_AES_256_GCM_SHA384, peer certificate: 2048 bit RSA, signature: RSA-SHA256
2022-11-15 21:37:37 [OpenVPN Server] Peer Connection Initiated with [AF_INET]192.168.239.133:1194
2022-11-15 21:37:38 MANAGEMENT: >STATE:1668519458,GET_CONFIG,,,,,,
2022-11-15 21:37:38 SENT CONTROL [OpenVPN Server]: 'PUSH_REQUEST' (status=1)
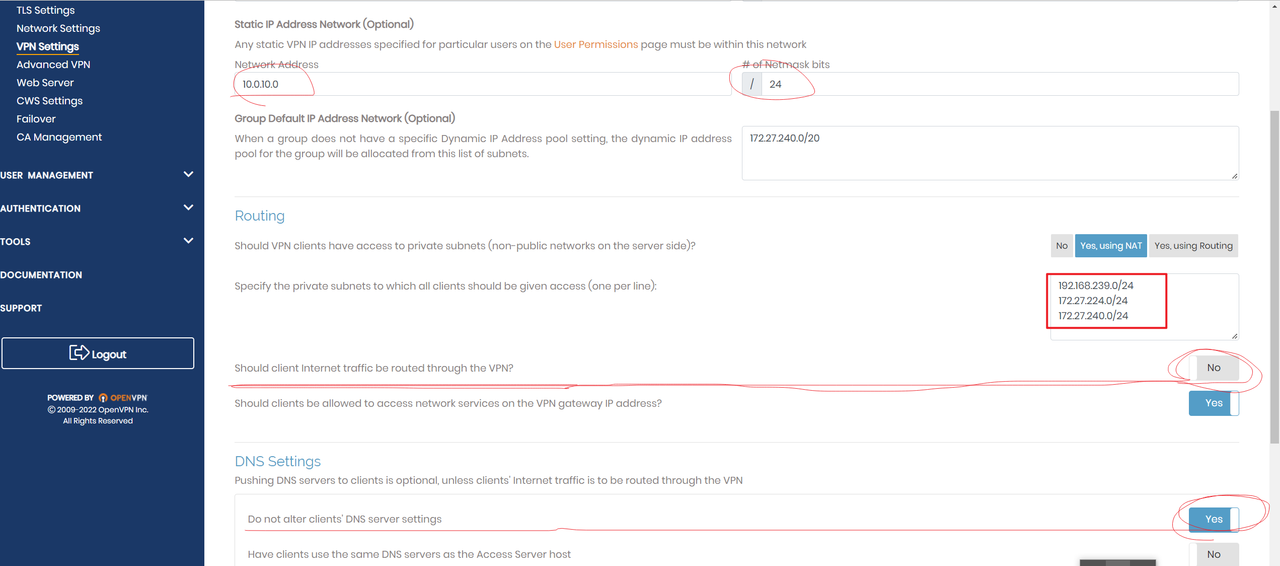
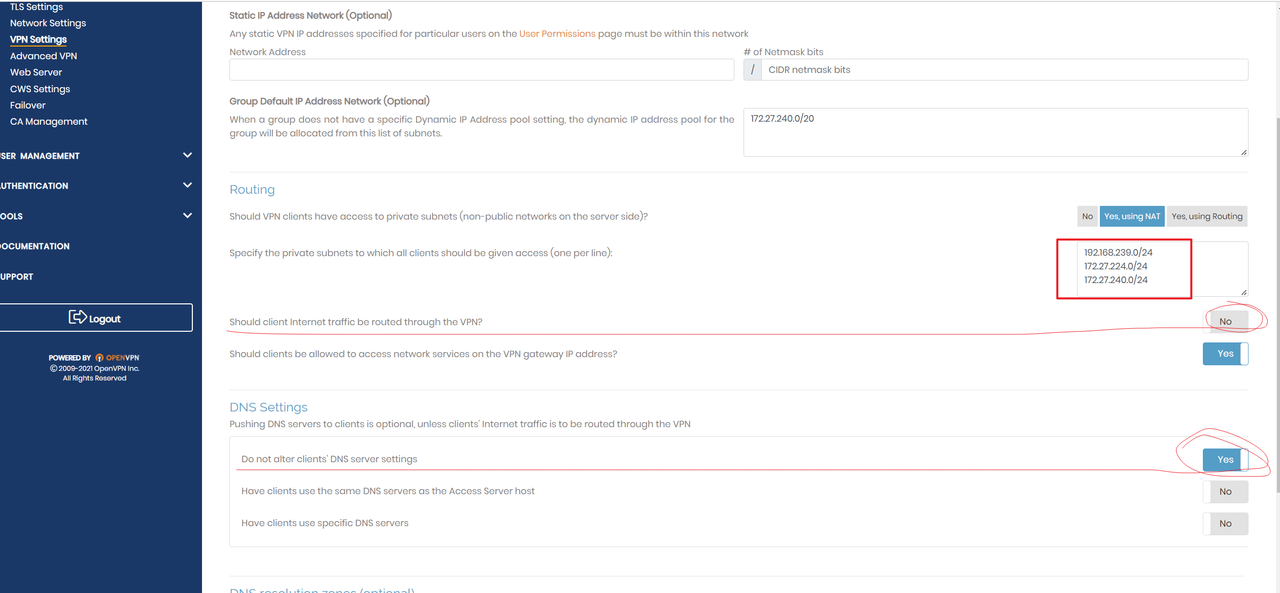
2022-11-15 21:37:38 PUSH: Received control message: 'PUSH_REPLY,explicit-exit-notify,topology subnet,route-delay 5 30,dhcp-pre-release,dhcp-renew,dhcp-release,route-metric 101,ping 12,ping-restart 50,redirect-private def1,redirect-private bypass-dhcp,redirect-private autolocal,redirect-private bypass-dns,route-gateway 172.27.232.1,route 172.27.240.0 255.255.255.0,route 192.168.239.0 255.255.255.0,route 172.27.224.0 255.255.240.0,block-ipv6,ifconfig 172.27.232.5 255.255.248.0,peer-id 1,auth-tokenSESS_ID,cipher AES-256-GCM'
2022-11-15 21:37:38 Obsolete option --dhcp-release detected. This is now on by default
2022-11-15 21:37:38 WARNING: You have specified redirect-gateway and redirect-private at the same time (or the same option multiple times). This is not well supported and may lead to unexpected results
2022-11-15 21:37:38 WARNING: You have specified redirect-gateway and redirect-private at the same time (or the same option multiple times). This is not well supported and may lead to unexpected results
2022-11-15 21:37:38 WARNING: You have specified redirect-gateway and redirect-private at the same time (or the same option multiple times). This is not well supported and may lead to unexpected results
2022-11-15 21:37:38 OPTIONS IMPORT: timers and/or timeouts modified
2022-11-15 21:37:38 OPTIONS IMPORT: explicit notify parm(s) modified
2022-11-15 21:37:38 OPTIONS IMPORT: --ifconfig/up options modified
2022-11-15 21:37:38 OPTIONS IMPORT: route options modified
2022-11-15 21:37:38 OPTIONS IMPORT: route-related options modified
2022-11-15 21:37:38 OPTIONS IMPORT: --ip-win32 and/or --dhcp-option options modified
2022-11-15 21:37:38 OPTIONS IMPORT: peer-id set
2022-11-15 21:37:38 OPTIONS IMPORT: adjusting link_mtu to 1624
2022-11-15 21:37:38 OPTIONS IMPORT: data channel crypto options modified
2022-11-15 21:37:38 Data Channel: using negotiated cipher 'AES-256-GCM'
2022-11-15 21:37:38 Outgoing Data Channel: Cipher 'AES-256-GCM' initialized with 256 bit key
2022-11-15 21:37:38 Incoming Data Channel: Cipher 'AES-256-GCM' initialized with 256 bit key
2022-11-15 21:37:38 interactive service msg_channel=628
2022-11-15 21:37:38 open_tun
2022-11-15 21:37:38 tap-windows6 device [OpenVPN TAP-Windows6] opened
2022-11-15 21:37:38 TAP-Windows Driver Version 9.24
2022-11-15 21:37:38 Set TAP-Windows TUN subnet mode network/local/netmask = 172.27.232.0/172.27.232.5/255.255.248.0 [SUCCEEDED]
2022-11-15 21:37:38 Notified TAP-Windows driver to set a DHCP IP/netmask of 172.27.232.5/255.255.248.0 on interface {22DD3C0C-75F0-4E7A-A383-975C46B5743A} [DHCP-serv: 172.27.232.0, lease-time: 31536000]
2022-11-15 21:37:38 Successful ARP Flush on interface [5] {22DD3C0C-75F0-4E7A-A383-975C46B5743A}
2022-11-15 21:37:38 TAP: DHCP address released
2022-11-15 21:37:38 TAP: DHCP address renewal succeeded
2022-11-15 21:37:38 MANAGEMENT: >STATE:1668519458,ASSIGN_IP,,172.27.232.5,,,,
2022-11-15 21:37:38 IPv4 MTU set to 1500 on interface 5 using service
2022-11-15 21:37:43 TEST ROUTES: 4/4 succeeded len=3 ret=1 a=0 u/d=up
2022-11-15 21:37:43 C:\Windows\system32\route.exe ADD 114.x.x.x MASK 255.255.255.255 192.168.1.1
2022-11-15 21:37:43 Route addition via service succeeded
2022-11-15 21:37:43 MANAGEMENT: >STATE:1668519463,ADD_ROUTES,,,,,,
2022-11-15 21:37:43 C:\Windows\system32\route.exe ADD 172.27.240.0 MASK 255.255.255.0 172.27.232.1 METRIC 101
2022-11-15 21:37:43 Route addition via service succeeded
2022-11-15 21:37:43 C:\Windows\system32\route.exe ADD 192.168.239.0 MASK 255.255.255.0 172.27.232.1 METRIC 101
2022-11-15 21:37:43 Route addition via service succeeded
2022-11-15 21:37:43 C:\Windows\system32\route.exe ADD 172.27.224.0 MASK 255.255.240.0 172.27.232.1 METRIC 101
2022-11-15 21:37:43 Route addition via service succeeded
2022-11-15 21:37:43 Initialization Sequence Completed
2022-11-15 21:37:43 MANAGEMENT: >STATE:1668519463,CONNECTED,SUCCESS,172.27.232.5,192.168.239.133,1194,,