Hello everyone,
So I want to give our contractors access to the services that they installed for us, but nothing else.
Our network subnet is 192.168.55.0/24
The specific devices address that the contractors need to access: 192.168.55.88 and 192.168.55.112, only
I found the Guide here: https://openvpn.net/community-resources ... -policies/
We installed the Open-AS on the Ubuntu Server by using automate script here: https://openvpn.net/vpn-software-packages/
and we are using mostly the web management interface to manage the OpenVPN-AS.
In this web interface, there is a session called "Additional OpenVPN Config Directives (Advanced)" and there is "Server Config Directives" and "Client Config Directives" text boxes. Is this where we insert the commands in the Guide above into?
I followed some other posts, which refer to modify the server.conf file but I was unable to find the server.conf file on my system. It was server.conf.gz file instead.
Any helps is appreciated
Thank you very much
Restricted Client access - How to input the commands?
-
jamesnb
- OpenVPN User
- Posts: 29
- Joined: Tue Sep 22, 2015 3:01 am
-
chilinux
- OpenVPN Power User
- Posts: 156
- Joined: Thu Mar 28, 2013 8:31 am
Re: Restricted Client access - How to input the commands?
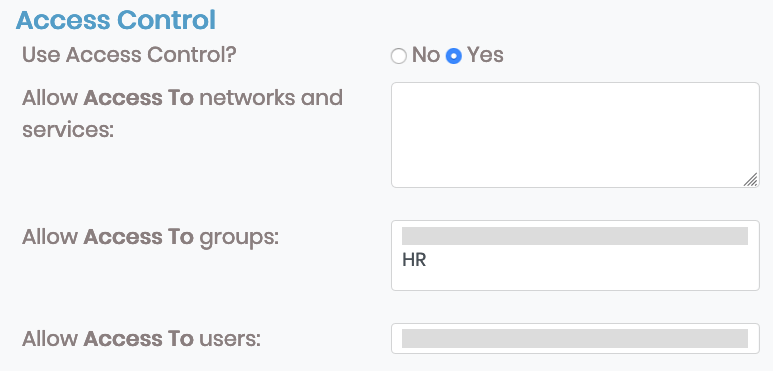
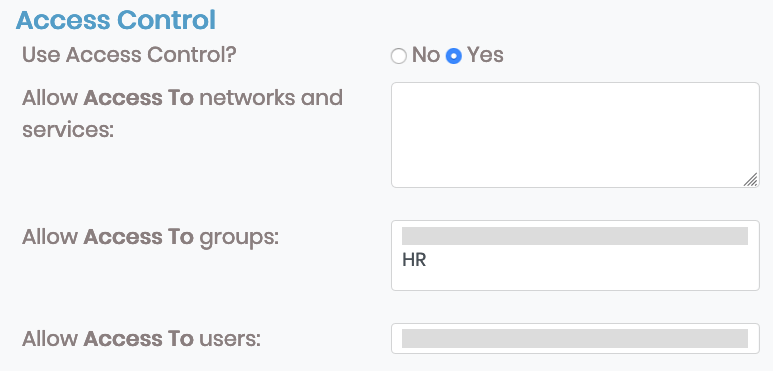
In OpenVPN AS admin panel:
1) Go to User Management
2) Then to Group Permissions.
3) Create your Contractors group
4) For the group, click on More Settings
5) Set Access Control to Yes
6) Under Allow Access To network and services put your specific IPs (and optionally specific network protocol/ports) such as:
192.168.55.88/32
192.168.55.112/32
7) Click Save Settings
8) Back under User Management go to User Permissions
9) Set each user you desire to the Contractors group
10) Click Save Settings
11) Click Update Running Server
I think this will do what you want.
1) Go to User Management
2) Then to Group Permissions.
3) Create your Contractors group
4) For the group, click on More Settings
5) Set Access Control to Yes
6) Under Allow Access To network and services put your specific IPs (and optionally specific network protocol/ports) such as:
192.168.55.88/32
192.168.55.112/32
7) Click Save Settings
8) Back under User Management go to User Permissions
9) Set each user you desire to the Contractors group
10) Click Save Settings
11) Click Update Running Server
I think this will do what you want.
- openvpn_inc
- OpenVPN Inc.
- Posts: 1333
- Joined: Tue Feb 16, 2021 10:41 am
Re: Restricted Client access - How to input the commands?
Hi There,
Chilinux is right. If the Access Control setting on OpenVPN Access Server is used, only specific subnets and services can be accessed by connected group members. To allow access to groups and users, you will need to manually input their IP address and include the proper services.
Access Control section:
Managing user or group-specific access control rules Specify an Access Control List for a user or group, allowing them to access one or more subnets on the server-side network by routing or NAT.
For example, to allow a user/group to access 192.168.4.0/24 and 10.10.0.0/24 via NAT:
Or to allow a user/group to only access TCP ports 80 or 443 from 10.10.0.0/24 via routing:
Or to allow a user/group to only access TCP ports 80 and 443, and UDP ports 2000-2999 on the specific IP addresses 10.10.0.2 and 10.10.0.5, via NAT:
As always, use ./confdba -us to see the current user/group properties. Here is the full reference for the Access Control model:
Allow user/group (or subnets routing through a VPN gateway authenticated as this user) to access these resources:
Allow these resources to access user IP (or subnets routing through a VPN gateway authenticated as this user)
A resource begins with '+' (allow) or '-' (deny), then continues with a type tag (such as 'USER', 'NAT', 'ROUTE', etc.) If the type requires additional parameters, the type tag is followed by a colon (':'), and type-specific data:
The optional SERVICES parameter is a comma-separated list of protocol/start_port[-end_port] values or well-known service names, e.g.:
This example allows access to/from the network 10.10.0.0/24, but only https (TCP 443), UDP 1194, TCP 1194, and UDP 2000-2999 traffic is allowed.
The current list of well-known service names include:
Crowley
Chilinux is right. If the Access Control setting on OpenVPN Access Server is used, only specific subnets and services can be accessed by connected group members. To allow access to groups and users, you will need to manually input their IP address and include the proper services.
Access Control section:
Managing user or group-specific access control rules Specify an Access Control List for a user or group, allowing them to access one or more subnets on the server-side network by routing or NAT.
For example, to allow a user/group to access 192.168.4.0/24 and 10.10.0.0/24 via NAT:
Code: Select all
./sacli --user <USER_OR_GROUP> --key access_to.0 --value "+NAT:192.168.4.0/24" UserPropPut
./sacli --user <USER_OR_GROUP> --key access_to.1 --value "+NAT:10.10.0.0/24" UserPropPut
./sacli startCode: Select all
./sacli --user <USER_OR_GROUP> --key access_to.0 --value "+ROUTE:10.10.0.0/24:tcp/80,tcp/443" UserPropPut
./sacli startCode: Select all
./sacli --user <USER_OR_GROUP> --key access_to.0 --value "+NAT:10.10.0.2:tcp/80,tcp/443,udp/2000-2999" UserPropPut
./sacli --user <USER_OR_GROUP> --key access_to.1 --value "+NAT:10.10.0.5:tcp/80,tcp/443,udp/2000-2999" UserPropPut
./sacli startAllow user/group (or subnets routing through a VPN gateway authenticated as this user) to access these resources:
Code: Select all
access_from.0 <resource1>
access_from.1 <resource2>Code: Select all
access_to.0 <resource1>
access_to.1 <resource2>Code: Select all
1. USER:<a user or group name>
2. NAT:<network>/<numbits>[:SERVICES]
3. ROUTE:<network>/<numbits>[:SERVICES]
4. ALL -- matches everything, i.e. 0.0.0.0/0
5. ALL_VPN_CLIENTS -- matches all IP addresses and subnets owned by all VPN clients
6. ALL_S2C_SUBNETS -- matches all server-side subnets as defined by vpn.server.routing.private_networkCode: Select all
+NAT:10.10.0.0/24:https,udp/1194,tcp/1194,udp/2000-2999The current list of well-known service names include:
Code: Select all
{
'ftp' : (('tcp', 21),),
'ssh' : (('tcp', 22),),
'smtp' : (('tcp', 25),),
'http' : (('tcp', 80),),
'pop3' : (('tcp', 110),),
'https' : (('tcp', 443),),
'imaps' : (('tcp', 993),),
'rdp' : (('tcp', 3389),),
}Regards,jamesnb wrote: ↑Sun Apr 11, 2021 6:05 pmHello everyone,
So I want to give our contractors access to the services that they installed for us, but nothing else.
Our network subnet is 192.168.55.0/24
The specific devices address that the contractors need to access: 192.168.55.88 and 192.168.55.112, only
I found the Guide here: https://openvpn.net/community-resources ... -policies/
We installed the Open-AS on the Ubuntu Server by using automate script here: https://openvpn.net/vpn-software-packages/
and we are using mostly the web management interface to manage the OpenVPN-AS.
In this web interface, there is a session called "Additional OpenVPN Config Directives (Advanced)" and there is "Server Config Directives" and "Client Config Directives" text boxes. Is this where we insert the commands in the Guide above into?
I followed some other posts, which refer to modify the server.conf file but I was unable to find the server.conf file on my system. It was server.conf.gz file instead.
Any helps is appreciated
Thank you very much
Crowley
Answers provided by OpenVPN Inc. staff members here are provided on a voluntary best-effort basis, and no rights can be claimed on the basis of answers posted in this public forum. If you wish to get official support from OpenVPN Inc. please use the official support ticket system: https://openvpn.net/support
