Cannot ping to client network from server side
Posted: Tue Mar 14, 2017 1:30 am
Hi OpenVPN Team,
I have installed OpenVPN to establish a Site to Site connection between two remotes networks
Here my Network schema
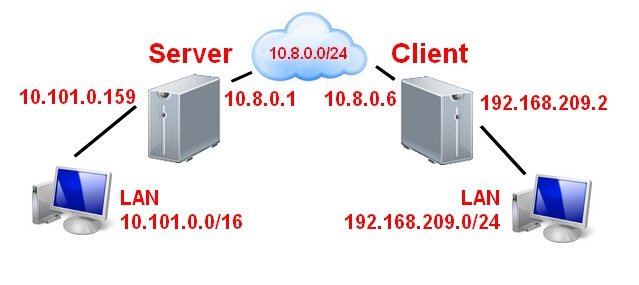
So I can ping the client side (192.168.209.0/24) to the server side (10.101.0.0/16) => OK
I can ping from the client side to 10.8.0.1 (server) => OK
And I can ping from the server side to 10.8.0.6 (client ) => OK
But I can't ping from server side to client network
For example from the server to the client machine => ping to 192.168.209.2 => Doesn't work
I enabled echo "1"> /proc/sys/net/ipv4/ip_forward
SERVER :
Here my server.conf
ip route
iptables -t nat -v -L
CLIENT
client.conf
ip route
iptables
When I'm on the server and i ping the client with tunnel IP 10.8.0.6
Here's the result with tcpdump on tun0
on the server
on the client
So it is ok it works
But When I'm on the server and I ping the client with his IP LAN 192.168.209.2
Here's the result with tcpdump on tun0
on the server
But Nothing on the client
It's the same when I'm make a ping trough the tunnel
like ping -I tun0 192.168.209.5, notthing append on the client side
How is it possible ? Can you help me please
Thank you in advance
I have installed OpenVPN to establish a Site to Site connection between two remotes networks
Here my Network schema
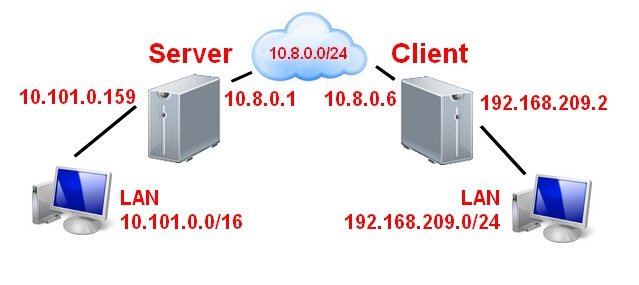
So I can ping the client side (192.168.209.0/24) to the server side (10.101.0.0/16) => OK
I can ping from the client side to 10.8.0.1 (server) => OK
And I can ping from the server side to 10.8.0.6 (client ) => OK
But I can't ping from server side to client network
For example from the server to the client machine => ping to 192.168.209.2 => Doesn't work
I enabled echo "1"> /proc/sys/net/ipv4/ip_forward
SERVER :
Here my server.conf
Code: Select all
port 1194
proto tcp
dev tun
ca keys/ca.crt
cert keys/xxx.crt
key keys/xxx.key
dh keys/dh2048.pem
server 10.8.0.0 255.255.255.0
ifconfig-pool-persist ipp.txt
keepalive 10 120
comp-lzo
persist-key
persist-tun
status openvpn-status.log
log openvpn.log
verb 3
Code: Select all
10.8.0.0/24 via 10.8.0.2 dev tun0
10.8.0.2 dev tun0 proto kernel scope link src 10.8.0.1
192.168.209.0/24 via 10.8.0.1 dev tun0 iptables -t nat -v -L
Code: Select all
Chain POSTROUTING (policy ACCEPT 150 packets, 23401 bytes)
pkts bytes target prot opt in out source destination
32 2664 MASQUERADE all -- any enp0s25 10.8.0.0/24 anywhere client.conf
Code: Select all
client
dev tun
proto tcp
remote xxxxxx 1194
resolv-retry infinite
nobind
persist-key
persist-tun
ca ca.crt
cert client.crt
key client.key
remote-cert-tls server
comp-lzo
verb 3Code: Select all
10.8.0.1 via 10.8.0.5 dev tun0
10.8.0.5 dev tun0 proto kernel scope link src 10.8.0.6
10.101.0.0/16 via 10.8.0.6 dev tun0
Code: Select all
Chain POSTROUTING (policy ACCEPT 31 packets, 2653 bytes)
pkts bytes target prot opt in out source destination
3 252 MASQUERADE all -- any tun0 192.168.209.0/24 anywhere
0 0 MASQUERADE all -- any ens4 10.101.0.0/16 anywhere
0 0 MASQUERADE all -- any ens4 10.8.0.0/24 anywhereWhen I'm on the server and i ping the client with tunnel IP 10.8.0.6
Here's the result with tcpdump on tun0
on the server
Code: Select all
02:18:47.922486 IP 10.8.0.1 > 10.8.0.6: ICMP echo request, id 7110, seq 39, length 64
02:18:47.934675 IP 10.8.0.6 > 10.8.0.1: ICMP echo reply, id 7110, seq 39, length 64Code: Select all
02:20:05.004943 IP 10.8.0.1 > 10.8.0.6: ICMP echo request, id 7110, seq 116, length 64
02:20:05.004980 IP 10.8.0.6 > 10.8.0.1: ICMP echo reply, id 7110, seq 116, length 64But When I'm on the server and I ping the client with his IP LAN 192.168.209.2
Here's the result with tcpdump on tun0
on the server
Code: Select all
02:21:26.057201 IP 10.8.0.1 > 192.168.209.2: ICMP echo request, id 7114, seq 7, length 64
02:21:27.057172 IP 10.8.0.1 > 192.168.209.2: ICMP echo request, id 7114, seq 8, length 64It's the same when I'm make a ping trough the tunnel
like ping -I tun0 192.168.209.5, notthing append on the client side
How is it possible ? Can you help me please
Thank you in advance